SimpleRisk has assessed our risk against the Apache Log4j vulnerability and determined that no customers deployed with our standard deployment instructions, regardless of On-Premise or Hosted environment, should be impacted by this vulnerability.
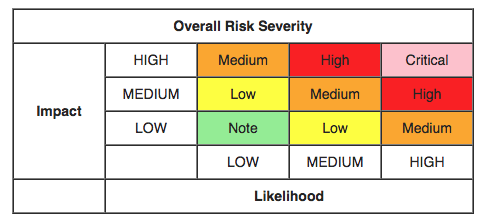
The OWASP Risk Rating Methodology and SimpleRisk
Over the years, we've received a number of inquiries about the OWASP Risk Rating Methdology with some contention around how we have integrated it into SimpleRisk. Some have questioned how SimpleRisk reaches its final risk score while others have pointed to differences in the Skill Level values. Let's delve into this...

Normalizing Risk Scoring Across Different Methodologies
If the "textbook" definition of risk scoring is Risk = Likelihood x Impact, then a Severe (5) impact and an Almost Certain (5) likelihood should have a score of 25, right? The answer isn't quite so simple...
How to Manage the Evolving Risk of Bluekeep (with SimpleRisk)
Unless you've been hiding under a rock for the past three weeks, you're probably familiar with CVE-2019-0708, also ...
Should Vulnerabilities and Risks be Managed in the Same Place?
While the distinctions between vulnerabilities versus risks has been widely documented in various forums, we ...


