Check out this recap of the webinar, "How to Model Security Maturity in Your Organization," co-hosted by SimpleRisk and GRC 20/20. This webinar helped equip participants with a clear roadmap on how to establish a security maturity baseline within their own organizations, create a desired state of maturity, and identify where gaps exist in order to achieve their objectives.

7 Strategies to Mature Your GRC Program
Check out this guest blog from Michael Rasmussen of GRC 20/20 to learn about seven strategies to mature your existing GRC program for enhanced efficiency and effectiveness.

6 Ways to Create a Repeatable, Scalable Compliance Program
Check out this guest blog from Michael Rasmussen of GRC 20/20 to learn about six core elements required to craft compliance programs that meet current standards and are adaptable and scalable to meet future compliance challenges and opportunities.

Getting Your Information Security Program Off the Ground
Struggling with where to begin with your Information Security Program? Learn how taking a risk-centric approach can help accomplish your goals.
8 Simple Ways to Effectively Launch Your GRC Program
Learn the 8 fundamentals we recommend to establish an effective Enterprise Risk Management process from the ground up, which will set the stage for a successful GRC program rollout.

The Right and Wrong Way to Assess Third-Party Risk
In this post, SimpleRisk's Founder and CEO walks us through the different approaches to assessing and managing third-party risks.
Responding to Inbound Risk Assessments with SimpleRisk
Learn how to use our Risk Assessment Extra to manage inbound assessments within SimpleRisk. Create a repeatable process without purchasing a separate tool.

How To Calculate Inherent vs. Residual Risk
Learn how to minimize the level of effort required to track a risk’s progress over time and how to measure the effectiveness of your risk mitigation.
Compliance 101: Back to Basics
Let’s go back to the basics and break down what enterprise compliance is and how you can use it to ensure your organization is conforming with its stated requirements.

The Impact of the Apache log4j Vulnerability (CVE-2021-44228) on SimpleRisk
SimpleRisk has assessed our risk against the Apache Log4j vulnerability and determined that no customers deployed with our standard deployment instructions, regardless of On-Premise or Hosted environment, should be impacted by this vulnerability.

Risk Management 101: Back to Basics
Let’s go back to the basics and break down what enterprise risk management is and how you can use it to mitigate the risks that threaten your organization.
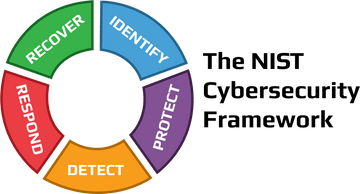
Simplifying the NIST Cybersecurity Framework with SimpleRisk
Learn how to use SimpleRisk's Import-Export and Risk Assessment Extras in order to efficiently use the NIST Cybersecurity Framework's controls to assess your organization's risks and perform a control gap analysis.

Risk Management for Dummies
Today I had a really interesting conversation with a guy from Japan via LinkedIn. It started with him trying to sell me...
There is Nothing Simple About FAIR
Currently, SimpleRisk supports six different risk scoring methods. We have Classic Risk, which is the likelihood ...
How to Perform Risk Assessments (with SimpleRisk)
This is just a short (1 minute) animated video explaining some of the capabilities around performing internal and ...
Assessing Vendor Security Risks (with SimpleRisk)
As a CISO for a large enterprise, many times my first engagement with members of our internal teams was when ...
What do Role Playing and Risk Management have in common?
A couple of weeks ago I participated in a CISO Summit with a focus on the topics of Security Visibility and Incident ...