In this blog, let’s go back to the basics and break down what enterprise compliance is and how you can use it to ensure your organization is conforming with its stated requirements. Our goal is to provide you with an effective compliance process that can help you identify and mitigate any potential risks.
What is enterprise compliance?
Enterprise compliance is an integrated approach to compliance that extends across multiple business units and locations within an organization. Enterprise compliance activities are designed to ensure an organization is compliant with relevant rules and regulations. Management will identify which requirements are applicable based on laws, regulations, contracts, strategies and policies. Once the applicable requirements have been identified, the organization then needs to assess the state of compliance with those requirements.
What is the goal of compliance?
Any areas where an organization is not meeting their requirements is considered a deficiency, which typically equates to a risk in their environment. The mitigation for these risks can then be prioritized against all of the organization's other initiatives. An effective compliance management program aims to ensure organization-wide compliance and protect organizations from a variety of risks. Check out our Risk Management 101 blog post for more information about how to mitigate any risks that you might identify when establishing your compliance program.
What are common questions to address when first establishing a compliance program?
- How do we identify requirements?
- Which control frameworks will we use?
- How do we protect our data?
- How do we validate the effectiveness of our compliance program?
- What tests are needed to validate controls?
- How often should audits be completed?
- Who is responsible for completing audits?
What are the steps in establishing a state of compliance?
1. Identify the applicable requirements.
The first stage of any Compliance program is to identify all of the applicable requirements. The list of requirements for a given organization can vary based on industry, geography, customers, etc. We typically recommend a data-driven approach to gathering your list of requirements. This means analyzing each of your organization's systems and processes in order to identify what kinds of data is stored or processed by each of them. The following are some of the more common types of data:
- Personally Identifiable Information (PII) - When used alone or with other relevant data, this data can be used to identify an individual. It may include direct identifiers, such as a social security number, driver’s license number or passport number. It also may include other information that when combined can successfully identify an individual, such as race, date of birth and address.
- Protected Health Information (PHI) - This is information about health status, provision of health care or payment for health care that is created or collected and can be linked to a specific individual. This includes any part of a patient's medical record or payment history.
- Cardholder Data - This is specifically related to the full payment card number, also known as a Primary Account Number (PAN), found on payment cards such as credit and debit cards. There are additional requirements on the Card Verification Value (CVV) found on many of these cards, as well.
- Customer Confidential Information - This is information that your organization is in possession of on behalf of a customer and is under a contractual Non-Disclosure Agreement (NDA) to keep that data secure.
- Company Confidential Information - This is information that your organization considers to be proprietary, a trade secret or information that could otherwise damage the organization's finances or reputation should it become public.
While this list isn’t all-inclusive, it does contain the more common types of data that many organizations identify, each of which will likely bring new requirements into scope. You should also discuss compliance with your Human Resources and Legal departments in order to ensure that you are taking all of the data into consideration and aren't leaving any gaps that could introduce risk at a later time.
2. Determine the requirements to protect the data.
Once you've identified what types of data you need to protect, the next step is to determine the requirements to protect that data. With the types of data outlined above, we frequently see the following control framework requirements identified (click the links below for additional information about how SimpleRisk caters to each type):
- Personally Identifiable Information (PII) - There are a large number of requirements around the protection of PII that end up being largely based on where an organization operates. For example, if you collect the PII from EU citizens, then you should be concerned with the General Data Privacy Regulation (GDPR).
- Protected Health Information (PHI) - The primary requirements around the protection of PHI in the United States stems from the Health Insurance Portability and Accountability Act (HIPAA).
- Cardholder Data - The Payment Card Industry (PCI) Security Standards Council is the organization responsible for the development, enhancement, storage, dissemination and implementation of security standards for account data protection. They have released the Data Security Standard (DSS) as a standard set of requirements around protecting cardholder data.
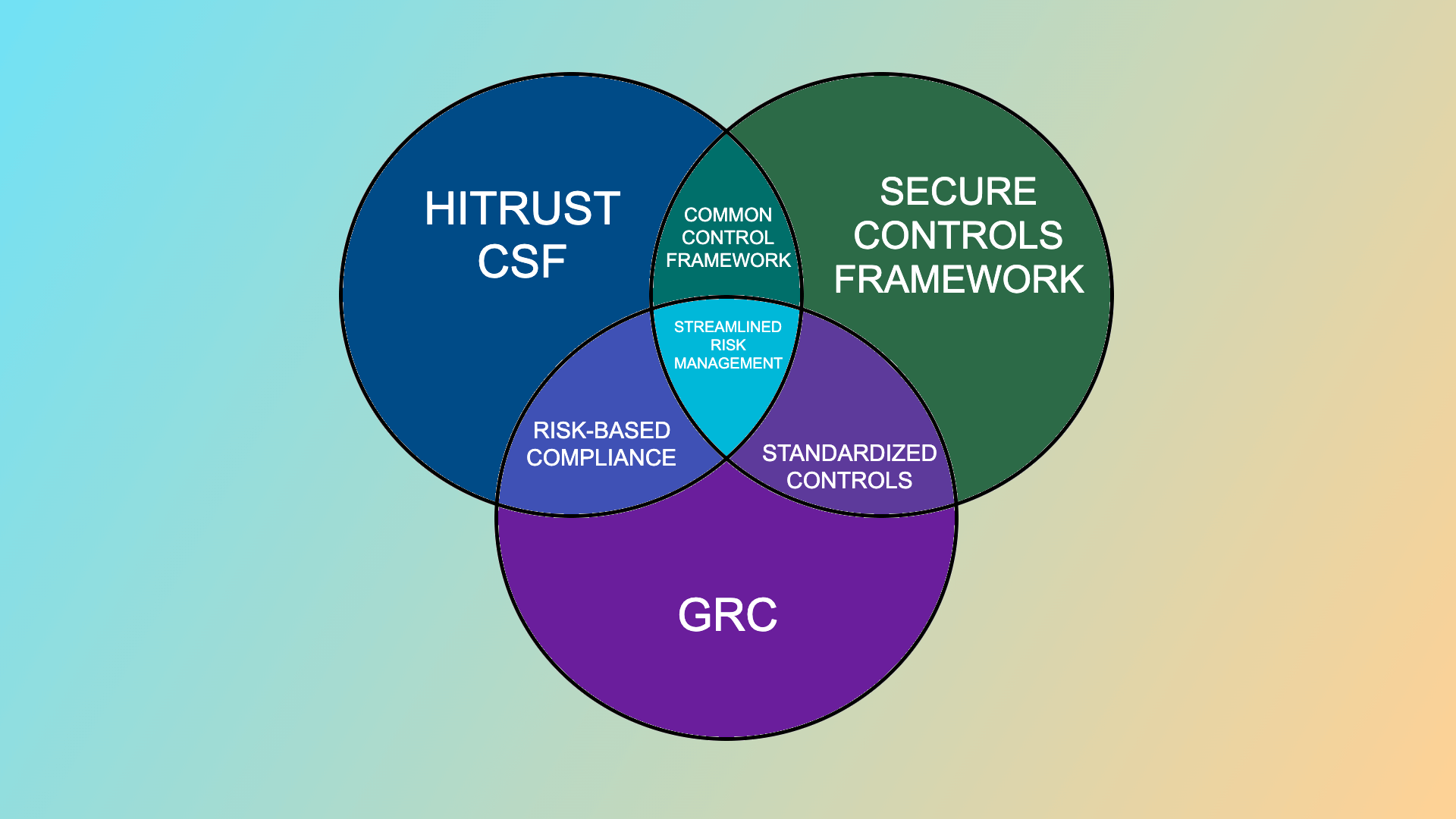
- Customer/Company Confidential Information - There is no universal framework that all organizations use for their privacy and security requirements around confidential information. For United States government organizations, we typically see the NIST Cybersecurity Framework (CSF), NIST Privacy Framework, and NIST SP 800-53 as the basis for their controls. For organizations handling data on behalf of the government, we frequently see the NIST CSF and NIST SP 800-171 as the required control frameworks. Outside of the United States, many countries have their own standards organizations which establish their own control frameworks such as the Australian Cyber Security Centre (ACSC), New Zealand Information Security Manual (NZISM), or Dubai Information Security Resolution (ISR). We've also seen a number of organizations adopt broader proprietary frameworks such as ISO 27001 and HITRUST to protect their confidential information.
3. Manage frameworks and controls.
After the frameworks that apply to an organization have been identified, those frameworks will need to be loaded into a GRC tool to manage the controls, validate their effectiveness and associate them with risks. On our Governance Solution page, we provide a step-by-step instructional on the different ways to load controls into SimpleRisk. While Governance is focused on documenting these frameworks, an organization's Compliance initiatives are going to focus on validating their effectiveness. This is where having a tool to manage your audits is extremely valuable.
4. Define tests to validate compliance.
When using a tool like SimpleRisk, your framework can be imported, and all of the controls will appear in the tool. From there, tests can be assigned to validate the controls. Each test should contain relevant information, such as a test name, test owner, test frequency and expected results.
5. Initiate an audit.
The test above acts as a template, describing the test and recording relevant information. It’s important from there to create an actual audit from the test. SimpleRisk manages every framework that has a control with a test associated with it. The framework can expand to show a list of all controls, and the controls can expand to show a list of all related tests. You can use this audit to initiate an audit on a full framework or on a specific control or test. Information can be included in the summary, documentation and evidence of ongoing testing can be attached, and comments can be added to the audit. Once the audit is completed, the Audit Status value can be updated to "Closed" and given a test result of "Pass,” "Fail" or "Inconclusive."
6. Report on compliance workflows.
Once an audit has been completed, you will need to report on your audit trail on a regular cadence in order to maintain your ongoing compliance. SimpleRisk has the ability to create a report that will show a list of all audits that have been conducted and highlight both the last time the test was conducted, the result of that test, and the next date a test is due. With each test, you'll have action buttons to initiate a new audit, view any currently active audits and view past audits. With our licensed Email Notification functionality, we are able to automate your audit workflows. As the audit statuses change or comments are added to them, this functionality will send notifications to key stakeholders about these actions taken within the system. Additionally, SimpleRisk can be configured to check on a daily basis for any audits that will soon be due based on a combination of the last time they were tested and the test frequency. You can configure automated notifications of these pending audits to email to key stakeholders at pre-defined intervals both before the due date and after the due date has been passed.
In conclusion, compliance, risk assessment and risk management are part of an ongoing process that requires significant tracking and analysis to be done efficiently in order to ensure organization-wide compliance. We hope this high level explanation has helped provide some insight into the steps involved in effectively managing compliance for your organization. For more information about how SimpleRisk can help establish your GRC program, visit our Compliance Solution page.
If you’d like to learn more about SimpleRisk or try it out for yourself, we offer several options:
- Download SimpleRisk Core and install in minutes to begin utilizing our free and open source platform.
- Start a 30 Day Trial for free unlimited access to your own dedicated instance of SimpleRisk with all of the SimpleRisk Extras.
- Schedule a Demo for a live demonstration of the application, covering topics such as using SimpleRisk to manage your risks, governance, compliance, risk assessment, and reporting.