In May of 2023, the infamous Cl0p ransomware gang added data theft to their resume with a SQL injection-based attack on Progress Software’s popular MOVEit file transfer app. Thousands of high-profile organizations, many in highly-regulated industries, had their sensitive data stolen in what became the year’s signature supply-chain hack.
As damaging as the MOVEit compromise was back then, perhaps the most insidious and enduring feature of the Cl0p attack is that the long-since-patched zero-day attack continues to ring up victims. That’s not because the mechanisms behind the breaches are mysterious or complicated. More than two years after victims like the BBC, British Airways, Ernst & Young, the U.S. Department of Energy, and the Louisiana Office of Motor Vehicles made headlines around the globe, there are organizations still vulnerable to the original MOVEit bug or still reliant on third-party systems that remain unpatched.
Getting pwned by old-ish vulns isn’t really a tech problem, it’s more an organizational shortcoming, a communication failure, to be precise. At some point in the lifecycle of every bug, every vulnerability notification, every compromise, every breach, it’s the security leaders who must not only inform the organization’s executives about the issue, they must also inspire them to act. For every organization still at risk of critical data loss due to bugs related to MOVEit vulnerabilities there’s a CISO who failed to impress the C-suite with the danger to the business and the harsh cost of inaction.
This remains true even when hacker shenanigans aren’t making headlines. When there’s new tools to consider, new skills to acquire, new security policies to implement, new investments in defense to make, it’s the CISO who’s charged with pitching the value of security to an audience of non-technical board members who speak dollars and cents, not speeds and feeds. When they fail, the consequences are familiar: flat budgets, delayed initiatives, and increased risk exposure.
CISOs aren’t losing budget battles because security isn’t important. They lose when security is explained poorly. Too many security conversations fail to adequately address the business outcomes boards are responsible for in a language that senior business decision makers can easily grok.
It’s long past time for all security leaders to take a page from the playbook of infosec’s most successful CISOs. If you really want to justify your security investments, both tactical and strategic, you a need strong c-suite game with presentation chops that map cyber-risk to business context in a way that wins business hearts, minds… and budgets.
Poorly Pitched Security Can’t Compete for Investment
A lot of CISOs come to the boardroom armed with important, if decidedly dry, metrics: vulnerability counts, alert volumes, patching SLAs, tool coverage, and on and on. From a technical standpoint, these numbers matter. From a business standpoint, though, they’re like a radio tuned between stations. Loud and mostly noise.
The first thing security leaders need to understand is that boards and executive teams make decisions based on trade-offs. They’re going to pit proposed security investments against gritty, tactile issues like revenue growth, operational efficiency, regulatory exposure, and strategic priorities. If security spending isn’t framed in those tangible terms, it’s perceived as a cost center rather than a risk-management function. The cost center loses every time.
The communication gap between CISOs and their bosses comes down to perspective. CISOs, by training, think in terms of threats, controls, technical outcomes. Board members and senior executives think in terms of financial impact, operational continuity, legal exposure, the company’s reputation. They don’t buy tools, they buy risk reduction. When an update from a CISO focuses on tools or tactics over impact and consequences, the message just isn’t going to land in the C-suite.
The results of this disconnect are predictable. Spending on poorly-framed security initiatives is thwarted. It turns into a reactive exercise with budgets only growing after the org gets punished by systems compromise and data loss. Preventative and defensive investments will always struggle to gain traction when their value isn’t clearly articulated in business language.
That’s made CISO-to-board communication one of the most critical and underdeveloped skills in cybersecurity leadership today. The ability to deftly translate security issues without oversimplifying is the one true talent that separates top-tier CISOs from the security hoi polloi.
Getting the Board on Board: Learning to Speak the Language of the Business
To justify cybersecurity budgets and investment effectively, CISOs must reframe their entire role, their raison d'être, if you will. They must identify as managers of business risk rather than simply defenders of infrastructure. How do you make this leap? Start by framing infosec issues in the form of questions boards truly care about: What could happen if a security control fails? How likely is that failure? What would it cost us as a company? How would it affect our customers, our operations, our partners, our regulatory standing?
Let’s look at some examples.
A CISO speaking to a technical audience might say:
“We have insufficient visibility into lateral movement across our environment, which increases dwell time if an attacker compromises a user account.”
Nothing untrue about that assertion. But in the boardroom, it’s too abstract. In the C-suite a better, more business-oriented version might be:
“If an attacker gets into our environment, we currently have limited ability to detect where they’ve gone and how deep the attack has penetrated into our systems. That increases the likelihood of prolonged disruption to the business and makes each incident much more expensive to contain.”
Same risk, different framing.
Another example, this time in a discussion of infosec tooling and staffing. The technical pitch is likely something like:
“Our SOC team is overwhelmed by alert volume, and we’re missing high-fidelity signals because we lack better correlation and automation.”
For an executive audience, a more effective translation would be:
“Our current monitoring approach creates too much noise, which slows our team’s response time during real incidents. The ROI for improved automation tooling will be realized through reduced downtime and markedly lower cost of recovery.”
Once again same issue, different lens.
One more from the governance and regulatory compliance front lines. It’s not uncommon to hear a security leader say something like:
“We need to automate our collection of controls evidence in order to reduce audit friction and address recurring findings.”
That’s fine for a security/GRC team meeting, but for the board, the better messaging puts the focus squarely on impact:
“Our current audit process consumes too much staff time and creates repeat findings that increase regulatory risk. Automating significant portions of the process will reduce audit costs and help us avoid costly penalties.”
What boards hear in our refined examples is a focus on operational risk, financial exposure, and efficiency gains with less time spent mulling and debating dry technical debt. Before any board-level discussion, ask yourself: If I removed all technical terms from this explanation, would the risk still be clear? If the answer’s no, the message needs reframing.
Practicing the Shift
Boards and executive teams are busy folks. They’re inundated with competing investment requests, every one of them claiming to be urgent. That’s why clarity of message for CISOs matters as much just as depth of detail.
Quantifying cyber risk takes consistency and context. When security risks are expressed in financial or operational terms like downtime costs, regulatory penalties, revenue impact, or customer churn, they’re easier to compare to other business risks. That comparison is what helps the C-suite make rational investment decisions. So, help them help you.
The following matrix shows how common infosec conditions can be better framed to solicit action from business decision makers. Over time, this communications shift helps the CSIO build credibility. Boards begin to see security as more than a collection of tools and threats, but as a disciplined approach to managing risk and uncertainty, and protecting business value.
The CISO Business Messaging Matrix
| Topic | Typical Tech Framing | Better Boardroom Version |
|---|---|---|
| Threat Detection and Monitoring | “We lack sufficient telemetry and correlation to detect advanced threats in real time.” | “We may not detect a serious breach quickly enough, which increases downtime, response costs, and potential customer impact.” |
| Vulnerability Management | “We have a backlog of high-severity vulnerabilities that haven’t been remediated within prescribed time frames.” | “Known weaknesses in our systems increase the chance of an incident that could disrupt operations or trigger regulatory scrutiny.” |
| Identity and Access Controls | “Over-permissioned identities and inconsistent access reviews create privilege escalation risk.” | “Too many users have more access than they need, increasing the risk of fraud, data exposure, or insider misuse.” |
| Incident Response Readiness | "Our incident response playbooks haven’t been fully tested across all business units.” | “If a major incident occurs, our response may be slower or less coordinated than it should be, increasing business disruption.” |
| Third-Party/Supply Chain Risk | “We have limited insight into the security controls of several critical vendors.” | “A security failure at a key vendor could expose our data or disrupt operations, even if our internal systems remain secure.” |
| Compliance and Audit Findings | “Manual evidence collection and control gaps are leading to inaccurate or redundant audit findings.” | “Our current compliance process increases audit costs and regulatory risk and also diverts staff from higher-value work.” |
| Security Tool Sprawl | “We have overlapping tools that aren’t well integrated, creating operational inefficiencies.” | “We’re spending money inefficiently and still carrying risk because our security investments are misaligned.” |
| Staffing and Skills Gaps | “We’re understaffed in key security functions and relying too heavily on manual processes.” | “We don’t currently have the capacity to manage risk effectively as the business grows, increasing exposure over time.” |
When CISOs can consistently communicate risk in these kinds of business terms, their role in the organization evolves. Their insights are primed to inform real, meaningful strategy. They become advisors rather than defenders. Partners more than petitioners.
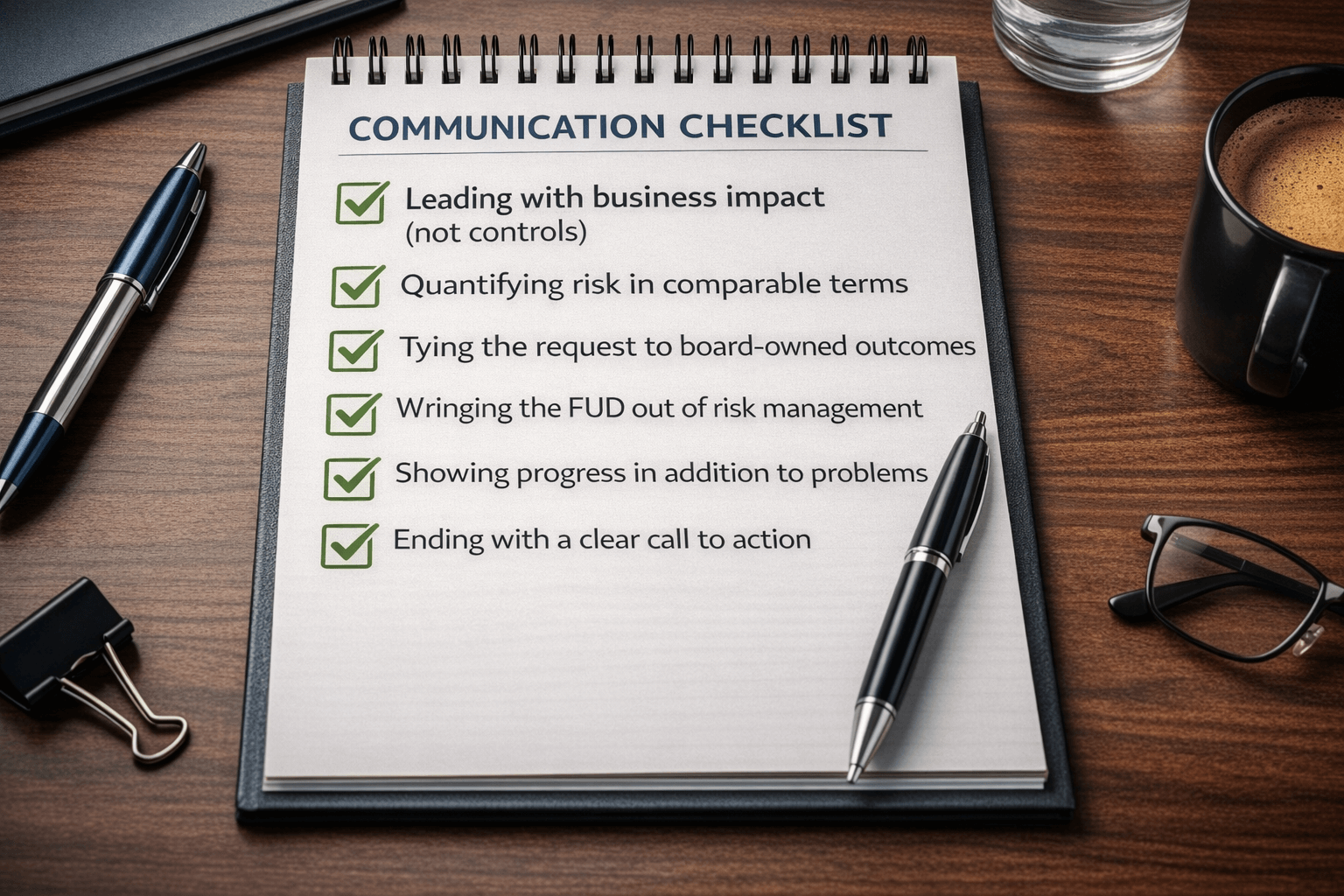
The CISO-to-Board Communication Checklist
Now that you’re committed to sharpening your security messaging for maximum impact in the C-suite, here’s a pre-meeting gut check for every security presentation on your plate. If your reports and pitches pass this muster every time, there’s a good chance your department is seen as a valued and productive member of the organization, worthy of respect, consideration and long-term investment. So, pull out your slide deck and ask yourself:
Leading with business impact (not controls)
- Can I explain this issue without name dropping any tools, frameworks, or acronyms?
- Have I clearly stated what happens to the business in the event of failure?
- Is the impact framed in terms of downtime, revenue, regulatory exposure, customer trust, or operational disruption?
Quantifying risk in comparable terms
- Have I translated risk into financial ranges, time-to-recovery, or operational impact metrics?
- Can this risk be compared alongside other non-technical business risks the board already evaluates?
- Have I avoided false precision while still giving executives something concrete to weigh?
Tying the request to board-owned outcomes
- Does my request clearly map to:
- System uptime?
- Improved regulatory compliance (or at least reduced legal exposure)?
- Better operational efficiency?
- Protection of revenue, brand value, or brand reputation?
- Can I articulate the cost of inaction as clearly as the price of action?
Wringing the FUD out of risk management
- Am I presenting this as a probabilistic risk (as opposed to a guaranteed catastrophe)?
- Does the message sound measured, credible, aligned with how executives discuss risk elsewhere in my organization?
- Am I avoiding sensationalism and vendor hype?
Showing progress in addition to problems
- Can I explain how this request fits into our long-term risk reduction strategy?
- Have I shown what’s been improved since our last update?
- Will executives leave knowing whether risk is increasing, stable, or decreasing?
Ending with a clear call to action
- Am I explicitly asking for:
- Approval?
- Funding?
- Prioritization?
- Risk acceptance?
- Is it clear and obvious what decision I want the board to consider right now?
Conclusion: Winning the Boardroom Battle
Many CISOs rose to their current position by mastering the wide array of technical systems and defensive controls that make up the broad discipline of information security. That and a healthy respect for the damage any failure of the CIA security triad can wreak (and probably a CISSP cert for good measure) served most CISOs well for decades.
But the game has changed, and today’s CISO needs to play by some new rules. For years, security leaders have begged corporate executives to see security as less of a cost center and more of a business advantage, a competitive differentiator. They got their wish. The result: CISOs now have a seat at the executive decision table. Now, CISOs need to optimize this opportunity, learning to who speak in business terms gain influence, trust, and funding from boards that prioritize risk management, resilience, and business continuity over tech talk and breach fear.
The communication makeover won’t happen overnight, and this isn’t a call to abandon technical rigor. A good CISO builds trust through clear translation and transparency. Boards come to trust the CISO who shows up every quarter with sharp, relevant risk narratives. They value strategic security presentations that explain both what’s happening in the environment, and why it matters to the business right now. Over time, this consistency builds credibility. CISO success is measured by how well they can shepherd security from reactive expense to strategic lever for organizational stability, growth, and confidence.
You never want to wait for incidents or emergencies to prove your value as a security leader. Start now by proactively connecting all of your current security investments to the outcomes your board is tuned into and accountable for: uptime, revenue protection, compliance, reputation, etc. A seat at the strategy table, and influence over security budgets, only comes with deep organizational engagement and fluency in the language of the business. Mastering these soft skills is now a prerequisite for true, competent security leadership.