About a week and a half ago, SimpleRisk went live with our Q3 2020 release. While this release included a handful of new features as well as bug and security fixes in the SimpleRisk Core, much of our attention in this go around went towards enhancing a number of our SimpleRisk Extras. The full release notes for this release can be downloaded here. What follows is a description of all of the new features, bug fixes and security fixes that were included in this new release.
SimpleRisk Core
For those who are unfamiliar with SimpleRisk's typical development process, I wrote this blog post which discusses how we typically prioritize items for our releases. What it doesn't really talk about is how we offer customers the ability to pay for their own enhancements to SimpleRisk. Several of the SimpleRisk Core enhancements in this release were driven with one of these custom development efforts from one of our customers out of New Zealand with the benefit of all customers now being able to take advantage of that functionality. These include:
- The introduction of a new "Settings" button which is included on the Plan Mitigation, Perform Reviews and Review Regularly pages under the Risk Management menu. When clicked, you will be able to select from a variety of different columns to have displayed on the report, enabling you to customize your views of this information.
- The addition of a filter for "Asset Tags" in the Risks and Assets report. Now, by assigning tags to assets, you can filter this report for a list of assets that belong to a specific category.
- The addition of a new "Printer" button which can be found at the bottom of the tables in the Dynamic Risk Report. When clicked, a new window will be displayed showing a printable view of the information displayed so that you can easily save it as a PDF or print it off for offline viewing.
The new release saw some enhancements made to how SimpleRisk handles sessions due to an issue discovered with the default hashing function configured for PHP on CentOS. This issue actually caused the session ID to be longer than the field used to store it in the database. While fixing this issue, we also added some debugging and function calls to increase visibility and consistency.
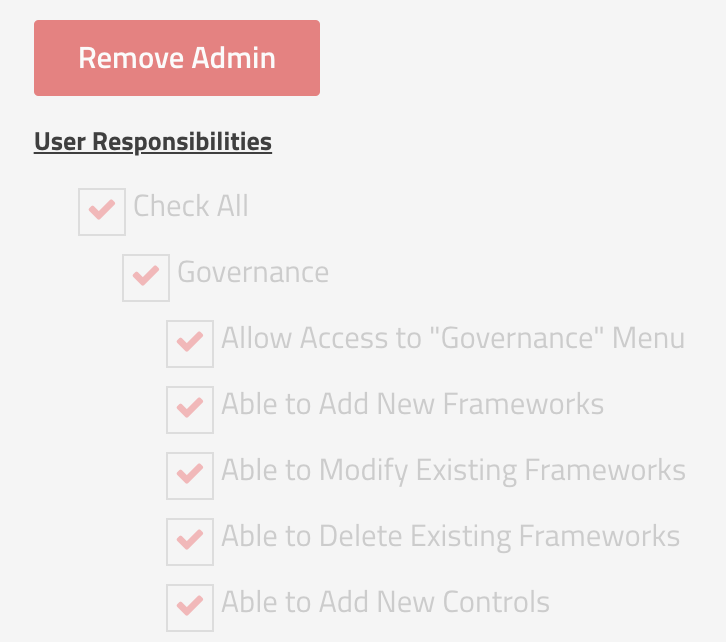
This release also included a major update to how permissions are handled in SimpleRisk. In the past, adding new permissions was a time-consuming effort as it involved adding new fields to the user table in the database. Now, we have a table that is dedicated to managing the permissions that are available. As part of this change, you will likely notice that we have removed the "Allow access to the Configure menu" responsibility for the user. This is because we realized that over time this had effectively become an "Administrator" role with abilities that extended beyond just access to a menu. As an example, users with this permission effectively belong to all teams and can see all risks. Now, you will see a very explicit "Grant Admin" button and users with this enabled will have all other permissions selected by default.
An issue that our support team saw fairly often in the past was where the healthcheck showed an error indicating that SimpleRisk was unable to communicate with the API while everything was working properly. This issue stemmed from what amounted to a poor check of the API functionality using native PHP calls. This check has been re-written to use curl, instead, to more accurately reflect the types of AJAX calls made by the application. Unfortunately, this also introduces a new dependency on the php-curl library for SimpleRisk to function properly. This support article will walk you through how to install that dependency on your system if you experience any issues related to it.
The last major update to the SimpleRisk Core with this release that I'd like to address is a change to how SimpleRisk handles our licensed SimpleRisk Extras. Unfortunately, we've had a couple of companies over the past few years who purchased SimpleRisk Extras, but then decided not to renew them, while continuing to utilize them. Our communications with them were ignored and, as an organization that thrives on building trust and partnerships with our customers, you can imagine how frustrating that would be. While not a persistent issue, it happened enough times that we decided to build some license checks into the software with this release. For the majority of our customers, this should be transparent and they will never be impacted by the change. The one exception is with customers who have locked down egress communications from their SimpleRisk server. These customers will either need to open up communication to services.simplerisk.com and ping.simplerisk.com on port 443 or enable a web proxy for these requests to route through under the "Security" tab in the Configure -> Settings menu.
Other new functionality added into the SimpleRisk Core with this release includes:
- Past audits are now ordered by both date & time as opposed to just date previously.
- Performing a review on a risk that is attached to a project will no longer remove the risk from that project.
- Updated the Register & Upgrade page to load faster and make fewer outgoing calls.
- Added a check to prevent duplicate control to framework mappings.
There were a number of bugs that were also addressed in this release:
- Fixed a bug that would leave an error after visiting the Governance pages.
- Fixed a bug where files added to audit tests would show on subsequent tests of the same kind.
- Removed upgrades for the Assessment Extra from the Core Upgrade scripts.
- Fixed an issue where sorting in the Risks and Assets report would be in Low to High order. It will now be in High to low as intended.
- Fixed an issue where various fields that draw data from multiple places would have a max character length that was not intended.
- Fixed an issue where users would not see tests to be initiated in the Compliance Initiate Test menu even though tests exist.
- Fixed an issue where users would receive an error while deleting a technology from “Add and Remove Values” in the “Configure” menu.
- Updated how the system determines if Extras are turned on or not to prevent various errors that could occur otherwise.
- Fixed an issue that could prevent users from adding new assets to the system in certain cases.
- Fixed an issue where images were unable to load with the Content Security Policy enabled.
- Corrected an issue where users would see multiple copies of a control for every framework it is mapped to when selecting mitigating controls in a risk mitigation.
- Fixed a bug where mitigating controls would not be displayed in certain situations.
- Fixed an issue filtering controls that were imported via the Compliance Forge SCF from being able to be queried and viewed in the Controls tab.
- Fixed an issue where the Define Tests page did not show mapped frameworks if there were tests associated with them.
- Fixed a few issues hindering the use of STRICT_TRANS_TABLES.
- Fixed an issue regarding upgrading from old versions from before 2020.
Security fixes included with this release include:
- Patched a vulnerability regarding debug logs.
- Fixed an XSS issue in Reporting.
SimpleRisk Extras
The SimpleRisk Extras are the paid for functionality that extend the features of the SimpleRisk Core. This release included a ton of new functionality and bug fixes to our SimpleRisk Extras:
Incident Management:
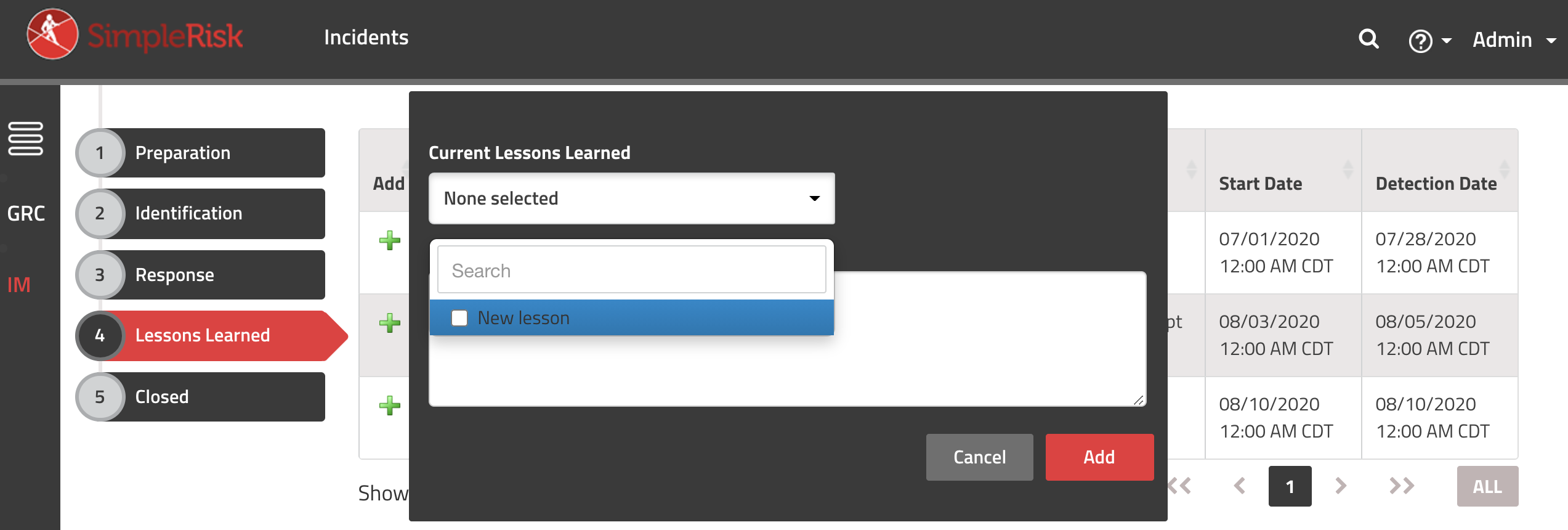
- Added the ability to associate incidents with Lessons Learned
- Added a "Closed" state for incidents
- Fixed a bug where each playbook was not treated as per incident.
Custom Authentication:
- The Custom Authentication Extra now supports the ability to select between sAMAccountName and userPrincipalName as the username attribute when using LDAP authentication.
- Users can now see the SAML 2.0 SP Metadata in the SAML Configuration section of the custom authentication extra.
Risk Assessment:
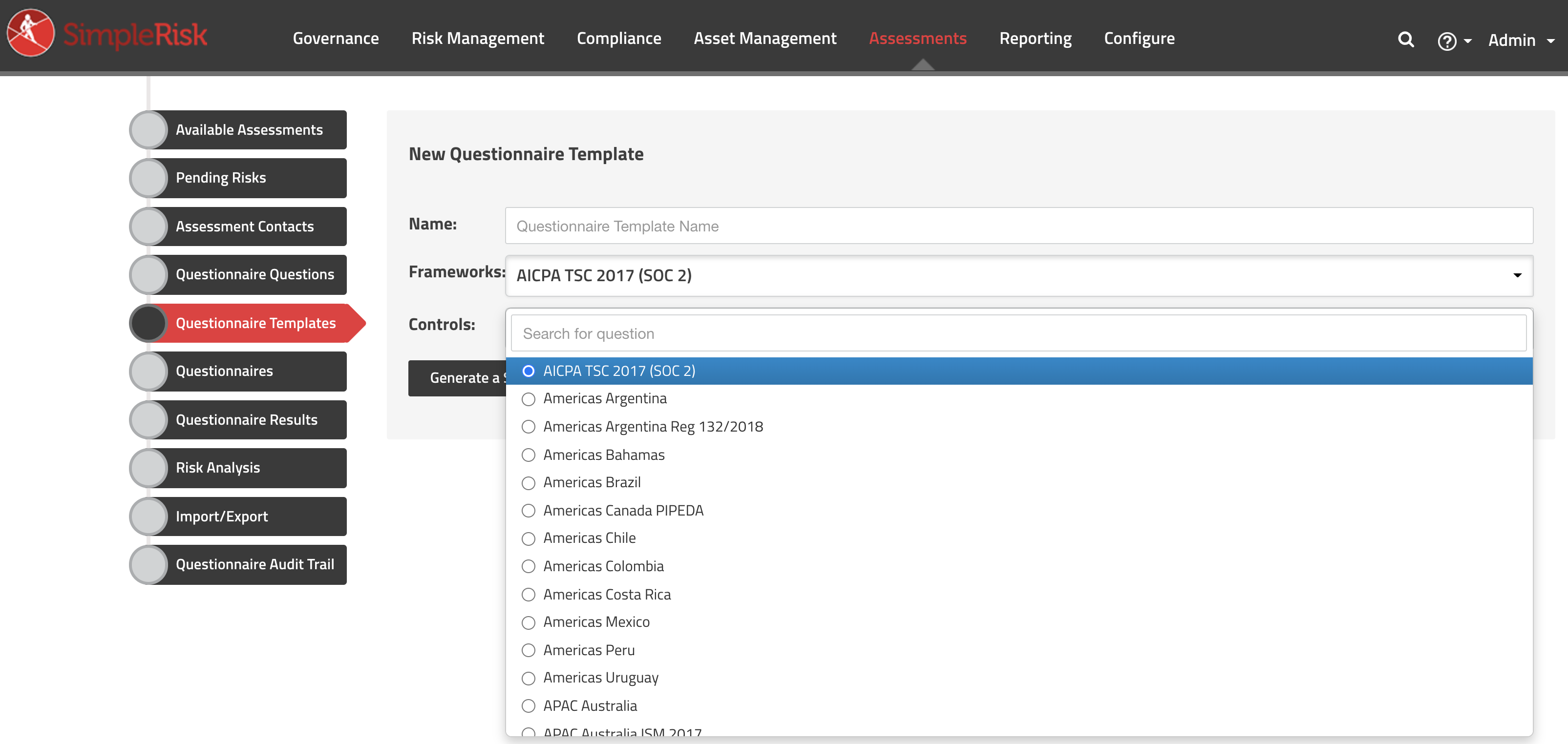
- Addition of a risk catalog linked to questionnaires and the Secure Controls Framework
- Additional Notes are now updated with Assessment Information
- Adding a pending risk from a questionnaire no longer refreshes the entire page.
- Added the ability to install and uninstall assessment templates from the GitHub repository with the click of a button.
- Added NIST Cybersecurity Framework (CSF) to the one-click assessment installation option.
- Added PCI DSS v3.2.1 Self-Assessment Questionnaire D for Merchants to the one-click assessment installation option.
- Fixed an issue where users could not assign contacts to questionnaires while using Internet Explorer.
Import-Export:
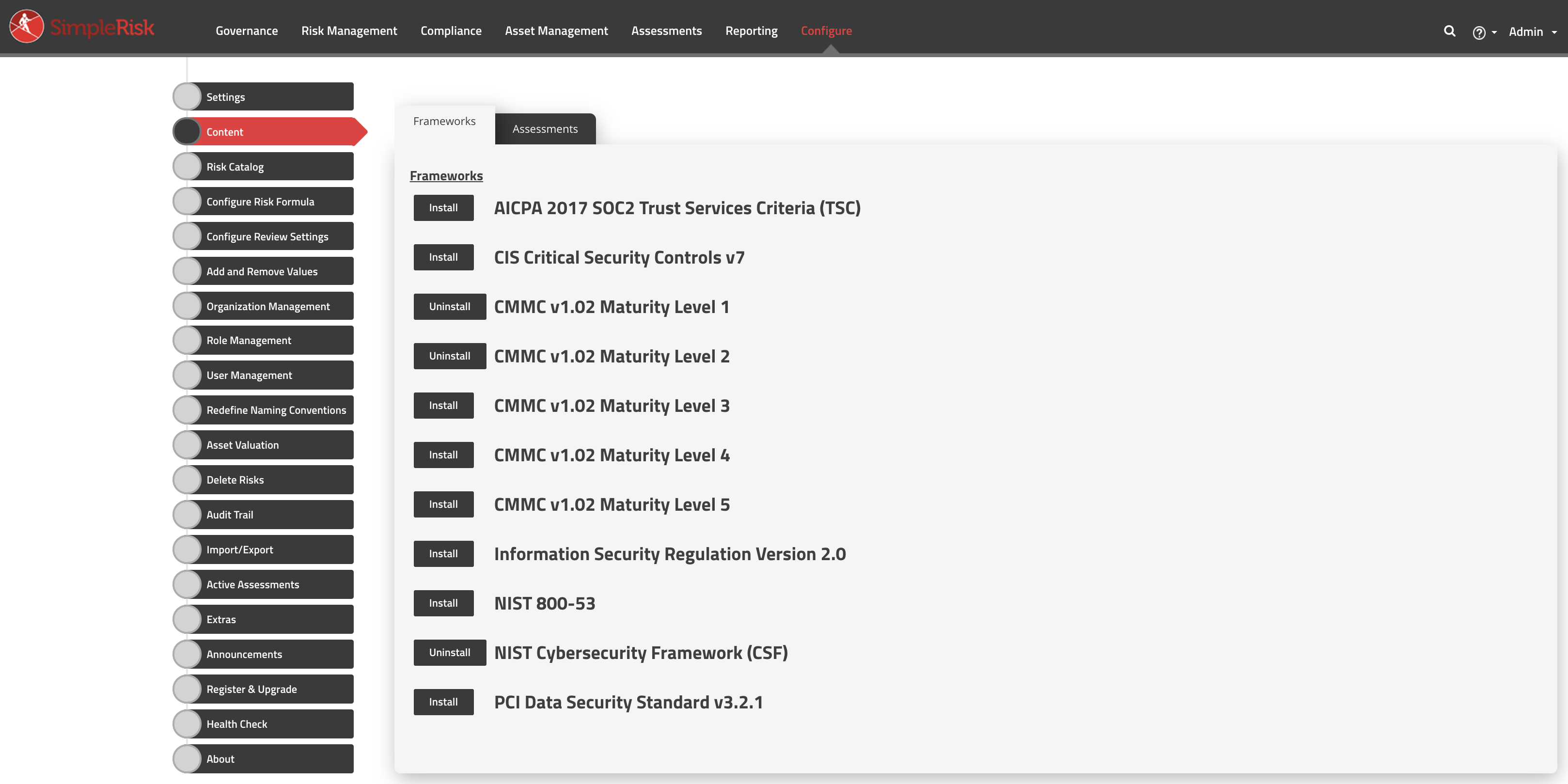
- Added the ability to install and uninstall frameworks from our GitHub repo with the click of a button through the import-export extra.
- Added AICPA 2017 SOC2 Trusted Services Criteria (TSC) to the one-click framework installation option.
- Added CIS Critical Security Controls v7 to the one-click framework installation option.
- Added CMMC v1.02 Maturity Level 1 to the one-click framework installation option.
- Added CMMC v1.02 Maturity Level 2 to the one-click framework installation option.
- Added CMMC v1.02 Maturity Level 3 to the one-click framework installation option.
- Added CMMC v1.02 Maturity Level 4 to the one-click framework installation option.
- Added CMMC v1.02 Maturity Level 5 to the one-click framework installation option.
- Added Information Security Regulation Version 2.0 to the one-click framework installation option.
- Added NIST 800-53 to the one-click framework installation option.
- Added NIST Cybersecurity Framework (CSF) to the one-click framework installation option.
- Added PCI DSS v3.2.1 to the one-click framework installation option.
Email Notification:
- Fixed an issue preventing scheduled notifications from being sent.
ComplianceForge SCF:
- Updated to display the SCF Control Number as part of the control short name and both the SCF Control Number and SCF Domain as part of the control long name.
- Overhauled several aspects of turning on the Compliance Forge SCF extra to decrease the time it takes to load into the system on the first activation.
- Removed the ability to delete Compliance Forge frameworks from the Governance pages.
Jira Integration:
- Creating a risk in SimpleRisk can now be set to open an issue in Jira.
Encryption:
- Fixed an issue where adding asset groups resulted in an encrypted audit log entry that was unable to be decrypted.