SimpleRisk Core
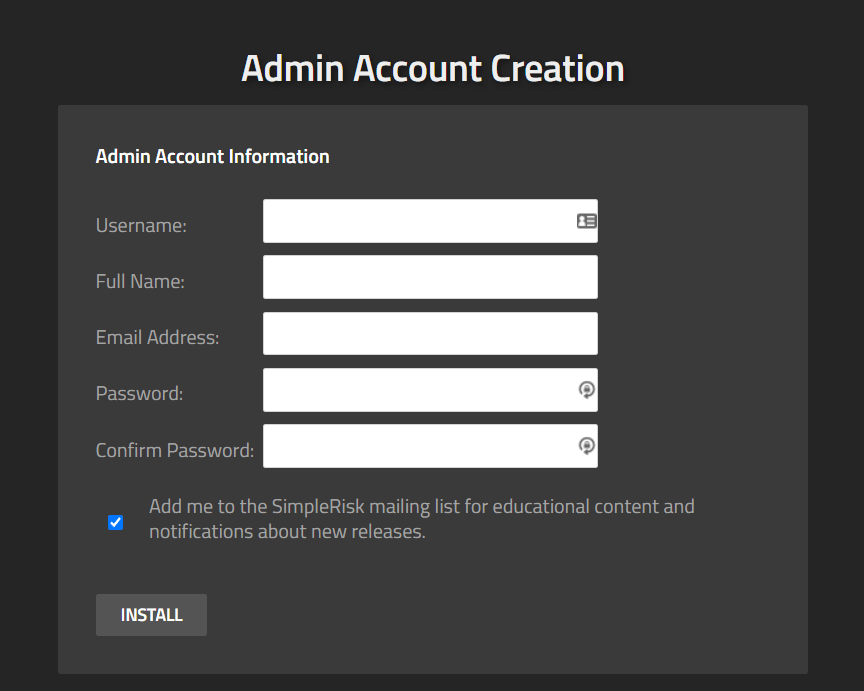
The SimpleRisk 20220401-001 release introduces a brand new installer. Users will no longer be required to download a separate bundle containing the installer code and default database schema. Now the installer is included with the SimpleRisk Core code and obtains the database schema directly from our repository. This new installation method also introduces the ability to customize the admin account during the database setup process. We will still include the ability to optionally download the installer separately as it was in the past while we transition documentation to the new method.
There were no other major features introduced in this release.
In our commitment to keeping SimpleRisk secure we have implemented a number of new security fixes in SimpleRisk which include:
- Fixed an information disclosure vulnerability.
- Fixed a vulnerability where users could view another user’s Graphical Risk Analysis saved report graphics.
- Moved phpspreadsheet for the Risk Assessments Extra to composer to update and patch a vulnerability with the old version, this change also applies to Import/Export as well.
- Fixed an XSS in the Incident Management Extra.
- Fixed an issue where a user could modify The Notification Extra configuration without permission to do so.
This release included a few much awaited bug fixes and are listed below:
- Fixed an issue where users could not sort by Planned Mitigation Date on the Dynamic Risk Report.
- We now suppress dumping GTIDs during backups. This will prevent the notice generally seen in the Apache log after a backup.
- Updated the query ran during the automated backup to correct a situation where this functionality would not operate as intended due to a lack of privilege on the MySQL user.
- Fixed an issue where attempting to filter on the Risk Mapping column in the Dynamic Risk Report would always return no results, even if it was selected from the dropdown.
SimpleRisk Extras
The SimpleRisk Extras are the paid for functionality that extend the features of the SimpleRisk Core. This is another release that targets bugs and security patches. One of the biggest fixes being for users who could not see custom fields while editing risks.
The full list of updates to Extras are as follows:
Customization Extra
- Multi-Select Dropdown field entries can now be deleted as intended.
- When restoring a risk template the threat mapping field will now also be restored.
- The Submission Date of risks will no longer be updated upon every update of a risk when the risk uses a template other than the default.
- Risk Mapping should no longer be doubled when activating Customization for the first time.
Vulnerability Management Extra
- Fixed a number of issues in the tenable.io implementation.
- Fixed a bug in the tenable.io connectivity test.
- Updated the tenable.io integration to ignore scans that are older than 35 days and have been archived.
- Updated tenable.io to only pull active sites.
- Updated the "Triage Vulnerabilities" page to display the number of vulnerabilities to triage.
- Updated the "View Risks" page to display the number of vulnerabilities that have been triaged into risks.
- Updated the "Triage Vulnerabilities" and "View Risks" pages to limit the initial description displayed to 500 characters and provide a "Read More" option to expand.
- Added a "platform" tag to risks created from Tenable.io.
- Added a log to show when the last run of Vulnerability Management was.
- Vulnerability Management Extra: Support for asset import from the Rapid7 InsightVM Cloud API.
Team-Based Separation Extra
- Added a suite of new permissions controls for different situations regarding the Document Program. You can now specify what attributes will give a user access to a given document including: User, Team, Stakeholders.
- Fixed an issue where non-admin users could not edit documents when the Team-Based Separation extra was active.
Incident Management Extra
- Fixed an issue where Incidents don’t display the Affected Assets dropdown on editing an incident when the Team-Based Separation extra is deactivated.
- Fixed an exploit where users could view risk titles by linking them to incidents.
- Added logic for related risks/assets so users who can edit the incidents can only edit the risks/assets they have access to.
- Fixed an XSS in the Incident Management extra on the reporting page.
- Fixed an issue where newly created playbooks could not be deleted without refreshing the page.
Import-Export Extra
- Fixed an issue where Management Review data would not import unless the status was mapped to “Mgmt Reviewed”.
Encryption Extra
- Assessment Sharing will now work with the Encryption Extra on.
- When sharing assessments with the Encryption Extra on users will no longer see encrypted names in audit entries for usernames.
- The print button will now function as intended when the Dynamic Risk Report is grouped by project. Users will no longer see encrypted data on the resulting printable version of the report.

